The explosive growth of digital technologies is spurring debates in the areas of data privacy and security. Despite the accelerating regulatory environments, it is only the tip of the privacy iceberg, both from a regulatory and consumer standpoint.
Three aspects come to the forefront. The first is the privacy-enhancing technology that provides a trusted environment in which sensitive data can be processed or analysed. The second performs processing and analytics in a decentralised manner. The third encrypts data and algorithms before processing or analytics. This approach is designed specifically for the increasing need to share data while maintaining privacy or security.
In the nearest future, privacy and data-centric security will have reached commodity status, with the ability for consumers to protect and control sensitive data assets becoming mainstream. While a global privacy standard may still be non-existent, at the organisational level a data-centric approach to security will transform from an add-on to the foundation of corporate strategy.
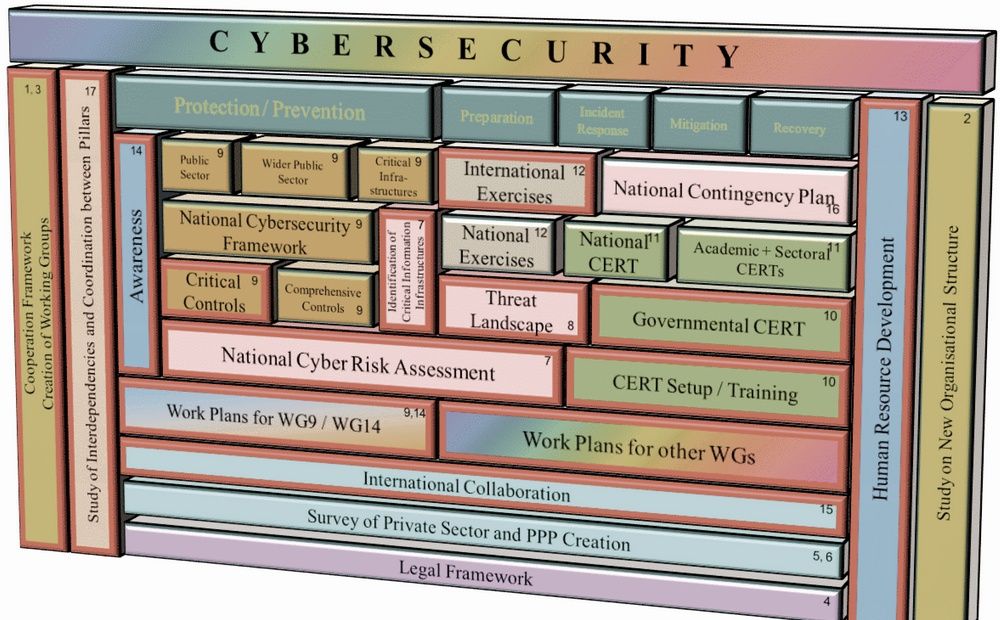
Cyprus adopted its National Cybersecurity Strategy in 2013. In 2018, it created the Digital Security Authority (DSA) and the national CSIRT team tasked with responding to the cybersecurity incidents in all critical infrastructures in the republic. The Security of Networks and Information Systems Law (the NIS Law) came into force on 12 August 2020, and covers operators of essential services, critical information infrastructure operators, electronic communications providers, and digital services providers.
Last autumn, Cyprus signed an agreement with the US to build a training facility to improve regional cybersecurity, along with border, port, and maritime security. Speaking of the latter, as of 1 January 2021, the International Maritime Organization’s Resolution 428(98) has come into force. It requires a vessel’s safety management systems to take into account cyber risk management. Considering that Cyprus manages the largest merchant fleet in the EU (1,734 ships in 2019), building a cybersecurity ecosystem for the shipping industry is one of the priorities for the DSA and the Deputy Ministry of Shipping.
PREDICTIONS OF EXPERTS FROM WWW.SECURITYMAGAZINE.COM (SUMMARY):
Remote workers will be the focus of cybercriminals through 2021.
Legacy security architecture like VPNs will be the weak link for many organisations.
To cope with reduced budgets, CSOs and CISOs will seek convergence across security solutions.
The impact of breaches in the healthcare sector may be deadly.
Financial organisations beware, more attacks are coming.
Covid-19 forced organisations to accelerate digital transformation efforts.
The adoption of new technologies and increase in internet users means most of the world’s population is at great risk of data exposure.
TWO MAIN TRENDS-2021 FROM FADY YOUNES, CYBERSECURITY DIRECTOR, MIDDLE EAST & AFRICA, CISCO
THE TIME FOR PASSWORDLESS
The password – the cornerstone and the Achilles’ heel of security. Passwords are troublesome to remember, rotate, and maintain, with an average person having 191 passwords. Passwords are also easily compromised, as 81% of breaches involve stolen credentials, according to the Verizon Data Breach Investigation Report. Technology has evolved which has made biometrics almost ubiquitous in both consumer and enterprise, and companies have begun to explore what a world without passwords will look like for users and data security.
ARTIFICIAL INTELLIGENCE, MACHINE LEARNING & ZERO TRUST SECURITY
In traditional security approaches, trust is based solely on the network location the access request originates from, while in a zero trust approach, trust is more dynamic and adaptive. It’s a network security model, established for every access request, no matter where it comes from, that secures access across apps and networks, and only allows the right users and devices to get access.
More authentication factors, adding encryption and marking known and trusted devices, make it harder for attackers to collect what they need (user credentials, network access, and the ability to move laterally). Purpose-built User and Entity Behaviour Analytics is one example how AI & ML can be used to help enable zero trust security. It places the analytics around specific activities rather than the generalised approach taken today.